How Many Social Engineering Indicators Are Present In This Email
Onlines
Apr 03, 2025 · 5 min read
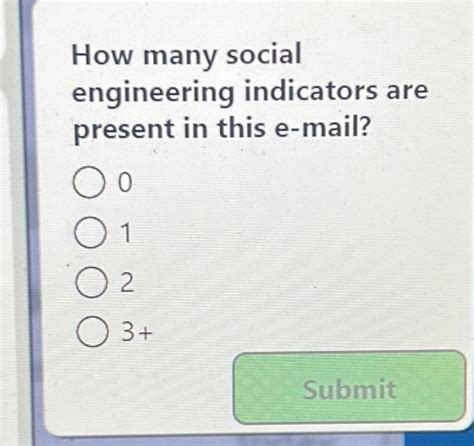
Table of Contents
Decoding Deception: A Deep Dive into Social Engineering Indicators in a Suspicious Email
The digital landscape is rife with malicious actors employing sophisticated techniques to gain unauthorized access to sensitive information. Social engineering, a manipulative tactic exploiting human psychology, is a cornerstone of many cyberattacks. Analyzing emails for social engineering indicators is crucial for protecting yourself and your organization from devastating breaches. This article will delve into a hypothetical email, dissecting its contents for various social engineering red flags. By understanding these indicators, you can significantly improve your ability to identify and avoid falling victim to these deceptive attacks.
The Suspicious Email:
Let's examine the following email:
Subject: Urgent: Your Amazon Account Security Alert!
Dear Valued Customer,
We have detected unusual activity on your Amazon account. To prevent unauthorized access and protect your personal information, please verify your account details immediately by clicking on the link below:
[Suspicious Link: http://amazon-security-verification.com/verify-account]
Failure to verify your account within 24 hours may result in its suspension. For your security, please do not reply to this email.
Sincerely,
The Amazon Security Team
Identifying Social Engineering Indicators:
This seemingly innocuous email is actually packed with several red flags indicative of a social engineering attack. Let's analyze them systematically:
1. Sense of Urgency and Fear:
-
Indicator: The email uses phrases like "Urgent," "immediately," and "within 24 hours." This creates a sense of panic, pressuring the recipient to act quickly without critically analyzing the message. Humans are more likely to make impulsive decisions under pressure.
-
Analysis: Legitimate companies rarely use such forceful language in their security communications. They understand that creating a calm and informative environment leads to better user engagement and cooperation.
2. Generic Greetings:
-
Indicator: The salutation "Dear Valued Customer" lacks personalization. Legitimate emails from companies usually address the recipient by name, enhancing trust and credibility.
-
Analysis: This generic approach suggests a mass-mailing campaign targeting numerous individuals. A personalized greeting would imply a more targeted and tailored communication.
3. Suspicious Link:
-
Indicator: The link provided,
http://amazon-security-verification.com/verify-account, is a classic example of a spoofed URL. Notice the subtle differences from the actual Amazon domain. -
Analysis: Legitimate companies use secure URLs that are typically HTTPS and match their official domain (e.g., amazon.com). The use of a slightly altered domain aims to trick users into believing it's authentic. Always hover over links to examine their destination before clicking.
4. Threat of Account Suspension:
-
Indicator: The email threatens account suspension if the verification isn't completed within 24 hours. This leverages the fear of losing access to a valuable service.
-
Analysis: While legitimate companies might notify users about suspicious activity, they usually provide more detailed information and options for resolving the issue, not an ultimatum.
5. Instruction Not to Reply:
-
Indicator: The instruction "please do not reply to this email" is suspicious. Legitimate companies usually provide multiple channels for communication and customer support.
-
Analysis: This instruction likely aims to prevent the recipient from seeking clarification or contacting Amazon directly to verify the email's authenticity.
6. Poor Grammar and Spelling:
-
Indicator: While not always present, poor grammar and spelling are often indicative of emails created by individuals with limited English language skills or those hastily crafted for a phishing campaign. In this example, the grammar is passable, but closer inspection might reveal subtler errors.
-
Analysis: Legitimate companies typically employ professional proofreaders to ensure their communications are error-free. Poor writing can be a clear sign that something is amiss.
7. Lack of Contact Information:
-
Indicator: The email lacks specific contact information beyond the ambiguous "Amazon Security Team." There's no phone number, physical address, or direct email address for contacting customer support.
-
Analysis: Legitimate companies usually provide multiple ways to contact their customer service departments. The absence of contact information makes it difficult to verify the email's authenticity.
8. Absence of Personal Account Details:
-
Indicator: The email doesn't include any specific details about the user's account (order numbers, recent purchases, etc.). This is a significant red flag.
-
Analysis: A legitimate security alert from a company like Amazon would likely reference specific aspects of the user's account to verify its authenticity. The lack of these details increases the likelihood of a phishing attempt.
9. Emotional Manipulation:
-
Indicator: The email employs emotional manipulation through fear and urgency to pressure the recipient into immediate action.
-
Analysis: Social engineers rely on emotions to bypass rational thinking. They prey on our fears of losing access to important accounts or facing financial consequences.
10. Domain Reputation:
-
Indicator: Researching the domain "amazon-security-verification.com" would reveal it's not a legitimate Amazon domain. Using online tools to check domain reputation is crucial.
-
Analysis: Legitimate companies have established online reputations. Checking the domain's age, registration details, and other online information can help to identify suspicious websites.
Conclusion:
The email analyzed above exhibits numerous social engineering indicators, making it highly suspicious. The combination of a sense of urgency, a generic greeting, a suspicious link, threats, lack of personalization, poor contact information, and other red flags strongly suggests a phishing attempt designed to steal the recipient's login credentials. By carefully examining these indicators and applying critical thinking skills, you can significantly improve your ability to recognize and avoid such deceptive emails. Remember, always verify the authenticity of any communication before taking action, especially if it involves sensitive personal information. Contact the company directly using official channels if you have any doubts about the email's legitimacy. Never click on links or open attachments from unknown or untrusted sources. Proactive vigilance is your best defense against social engineering attacks.
Latest Posts
Latest Posts
-
The Land Ethic Aldo Leopold Summary
Apr 04, 2025
-
A Farewell To Arms Quotes With Page Numbers
Apr 04, 2025
-
Which Disorder Would The Nurse Classify As Neurodevelopmental
Apr 04, 2025
-
Loss Grief Death Hesi Case Study
Apr 04, 2025
-
Summary Of The Book Of The City Of Ladies
Apr 04, 2025
Related Post
Thank you for visiting our website which covers about How Many Social Engineering Indicators Are Present In This Email . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
