Privacy At Dhs Protecting Personal Information Test Answers
Onlines
Apr 05, 2025 · 5 min read
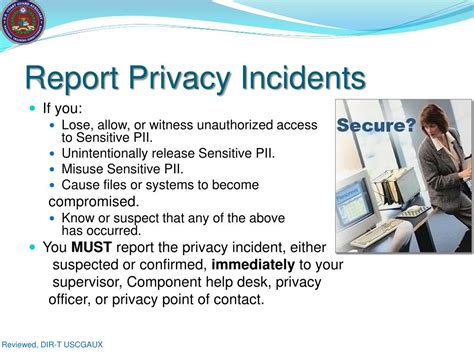
Table of Contents
Privacy at DHS: Protecting Personal Information – A Comprehensive Guide
The Department of Homeland Security (DHS) handles vast amounts of sensitive personal information daily, making data privacy a paramount concern. This article delves into the multifaceted approach DHS employs to protect this information, covering policies, technologies, and ongoing challenges. We'll explore the intricacies of data protection within the context of testing and assessments, ensuring a comprehensive understanding of this crucial aspect of national security and individual privacy.
Understanding DHS's Data Protection Mandate
DHS's mission inherently involves collecting and processing personal data. This data, ranging from immigration applications to transportation security screenings, requires robust protection against unauthorized access, use, disclosure, disruption, modification, or destruction. The department's commitment to privacy isn't merely a compliance exercise; it's fundamental to maintaining public trust and ensuring the effectiveness of its critical missions.
Key Legislation and Regulations
Several key pieces of legislation and regulation guide DHS's data protection efforts. The Privacy Act of 1974 is a cornerstone, restricting the collection, use, and disclosure of personal information by federal agencies. The Freedom of Information Act (FOIA) allows public access to certain government information, while carefully balancing transparency with the need for protecting sensitive data. Furthermore, the Digital Millennium Copyright Act (DMCA) and various other regulations related to cybersecurity and information security play significant roles in shaping DHS's data protection framework.
DHS's Internal Policies and Procedures
Internally, DHS maintains a comprehensive set of policies and procedures designed to safeguard personal information. These internal directives cover areas such as:
- Data Minimization: Collecting only the necessary data for specific purposes.
- Data Security: Implementing robust technical and physical security measures to protect data from unauthorized access.
- Data Retention: Establishing clear guidelines on how long personal data is retained and securely disposed of after its intended use.
- Data Breach Response: Developing and regularly testing procedures to effectively respond to and mitigate data breaches.
- Employee Training: Providing comprehensive training to all employees on data privacy and security best practices.
These internal policies are rigorously enforced and regularly reviewed to adapt to evolving threats and technological advancements.
Protecting Personal Information in DHS Testing and Assessments
The context of testing and assessments within DHS adds another layer of complexity to data privacy considerations. Various assessments, including background checks, security clearances, and performance evaluations, necessitate handling sensitive personal information. Protecting this data during these processes is critical.
Data Encryption and Anonymization
DHS utilizes advanced encryption techniques to safeguard data both in transit and at rest. Encryption transforms data into an unreadable format, protecting it from unauthorized access even if a breach occurs. Anonymization techniques, where identifying information is removed or masked, are employed where feasible to further protect individuals' privacy.
Access Control and Authentication
Strict access control measures are in place to limit access to sensitive personal information only to authorized personnel on a need-to-know basis. Multi-factor authentication, requiring multiple forms of verification (e.g., password and one-time code), enhances security and prevents unauthorized access. Regular audits of access logs are conducted to detect and prevent any suspicious activity.
Secure Data Storage and Disposal
DHS employs secure data storage solutions, including encrypted databases and secure cloud storage, to protect personal information. Data disposal procedures ensure that personal data is securely erased or destroyed when no longer needed, preventing unauthorized access or retrieval.
Addressing the Challenges of Data Privacy at DHS
Despite the extensive measures in place, DHS faces several ongoing challenges in protecting personal information:
The Ever-Evolving Threat Landscape
Cybersecurity threats are constantly evolving, making it crucial for DHS to adapt its security measures to counter emerging threats. This necessitates continuous investment in new technologies, employee training, and threat intelligence.
Balancing Security with Operational Efficiency
Maintaining robust security measures while ensuring operational efficiency can be a delicate balancing act. Overly restrictive security measures can hinder the timely completion of essential tasks, while insufficient security can expose sensitive information to risk. Finding the right balance is paramount.
Data Breaches and Their Consequences
Data breaches, even with robust security measures in place, remain a possibility. The consequences of a data breach can be significant, including reputational damage, legal liabilities, and loss of public trust. Therefore, robust incident response plans are essential to mitigate the impact of any potential breach.
The Volume and Variety of Data
The sheer volume and variety of data handled by DHS present a significant challenge. Managing and protecting this data effectively requires sophisticated tools and technologies, along with a well-defined data governance framework.
The Future of Data Privacy at DHS
DHS is actively working to enhance its data privacy and security capabilities. This involves:
- Investing in advanced technologies: This includes artificial intelligence (AI) and machine learning (ML) for threat detection, blockchain technology for enhanced data security, and quantum-resistant cryptography to prepare for future computing advancements.
- Strengthening collaboration: Collaborating with other government agencies, private sector organizations, and international partners to share best practices and enhance collective security.
- Promoting transparency and accountability: Continuously improving transparency regarding its data protection efforts and holding itself accountable for any shortcomings.
The future of data privacy at DHS relies on a proactive, adaptable approach, constantly evolving to meet the challenges of a rapidly changing technological landscape.
Conclusion
Protecting personal information is a cornerstone of DHS's mission. The department's commitment to privacy is reflected in its comprehensive policies, robust security measures, and ongoing efforts to adapt to evolving threats. While challenges remain, DHS's dedication to safeguarding sensitive data is essential for maintaining public trust and ensuring the effectiveness of its vital security functions. The ongoing investment in technology, training, and collaboration ensures a future where data privacy is not just a priority, but a foundational element of national security. This commitment is crucial not only for protecting individuals but for upholding the integrity of the department's critical missions. The constant adaptation and proactive approach are key to success in this dynamic field. Furthermore, ongoing evaluation and improvement of internal procedures and external collaborations are vital for enhancing the overall effectiveness of DHS's data protection efforts. The future of data privacy at DHS depends on this continuous evolution and commitment to excellence.
Latest Posts
Latest Posts
-
Characters In Never Let Me Go
Apr 05, 2025
-
Which Of The Following Is Not An Agent Of Erosion
Apr 05, 2025
-
A Neutral Friendly Nation Has Expressed
Apr 05, 2025
-
Genesis Concludes With Israel In Canaan
Apr 05, 2025
-
Labeling Exercise 7 2 Tube Stopper Colors And Order Of Draw
Apr 05, 2025
Related Post
Thank you for visiting our website which covers about Privacy At Dhs Protecting Personal Information Test Answers . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
