3.11.1 Packet Tracer - Network Security Exploration
Onlines
Apr 02, 2025 · 6 min read
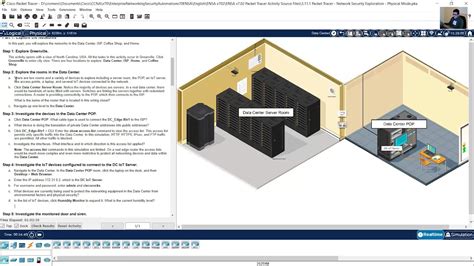
Table of Contents
3.11.1 Packet Tracer: A Deep Dive into Network Security Exploration
Packet Tracer, Cisco's powerful network simulation tool, offers invaluable hands-on experience for aspiring network engineers. Version 3.11.1, while slightly older, still provides a robust platform to explore fundamental network security concepts. This comprehensive guide will delve into various security scenarios you can simulate and learn from using Packet Tracer 3.11.1, focusing on practical application and theoretical understanding. We’ll cover everything from basic firewall configurations to more advanced topics like intrusion detection and prevention.
Understanding the Basics: Setting Up Your Secure Network
Before diving into complex security measures, it's crucial to understand the foundational elements. In Packet Tracer 3.11.1, you'll build your network using virtual devices like routers, switches, and end devices (computers). The arrangement of these devices and their configurations determine your network's security posture.
1. Network Segmentation: The First Line of Defense
Network segmentation involves dividing your network into smaller, isolated sections (VLANs – Virtual Local Area Networks). This limits the impact of a security breach. If a hacker compromises one segment, they won't automatically gain access to the entire network. In Packet Tracer, you can create VLANs on your switches and assign ports to specific VLANs, effectively isolating different parts of your network.
2. Access Control Lists (ACLs): Filtering Network Traffic
ACLs are like gatekeepers, controlling what traffic is allowed to pass through your network. They can be configured on routers and switches to filter traffic based on various criteria, including source and destination IP addresses, ports, and protocols. Experiment with creating different ACLs in Packet Tracer to block unwanted traffic, such as specific websites or ports commonly used for malicious activities. Practice creating both inbound and outbound ACLs to truly grasp their functionality. Understanding the difference between implicit deny and explicit deny is critical.
3. Firewalls: The Bulwark Against Threats
Firewalls act as a barrier between your network and the outside world. They examine network traffic and block anything that doesn't match predefined rules. In Packet Tracer 3.11.1, you can simulate different firewall types, understanding their strengths and weaknesses. Experiment with configuring stateful firewalls, observing how they track connections and allow return traffic. Compare this behavior to that of a stateless firewall. Consider scenarios where different firewall rules interact, leading to unexpected outcomes. This will strengthen your understanding of firewall rule prioritization.
Exploring Advanced Security Concepts
Once comfortable with the fundamentals, you can explore more advanced security concepts within the limitations of Packet Tracer 3.11.1. These simulations will help solidify your understanding of real-world network security challenges.
1. Intrusion Detection Systems (IDS): Monitoring for Anomalies
An IDS monitors network traffic for malicious activity. While Packet Tracer might not have a dedicated IDS device, you can simulate its functionality by closely observing network traffic using Wireshark (or a similar tool if integrated) and analyzing patterns. Set up a scenario where you simulate a denial-of-service (DoS) attack. Observe the network traffic and try to identify the attack signature. This exercise helps you understand how an IDS works and the importance of analyzing network traffic for anomalies.
2. Virtual Private Networks (VPNs): Secure Remote Access
VPNs create secure connections over public networks, encrypting data to protect sensitive information. While Packet Tracer 3.11.1 might not have the full functionality of a commercial VPN solution, you can simulate the concept by establishing secure connections between devices using IPSec or other encryption methods (if supported in your version). Experiment with different encryption protocols and observe the impact on performance and security.
3. Wireless Security: Protecting Your Wireless Network
Wireless networks are particularly vulnerable to attacks. In Packet Tracer, you can simulate a wireless network and configure various security protocols, such as WPA2 or WPA3 (if available). Compare the security strengths and weaknesses of different wireless encryption protocols. You can also simulate attacks like dictionary attacks against weak passwords to understand the importance of strong passwords and robust security protocols.
Hands-On Scenarios and Exercises
To solidify your learning, consider these practical exercises within Packet Tracer 3.11.1:
-
Scenario 1: Building a Secure Home Network: Create a home network with multiple devices (computers, smartphones, IoT devices). Segment the network using VLANs and implement ACLs to control access to specific devices and resources. Configure a firewall to protect the network from external threats.
-
Scenario 2: Simulating a Man-in-the-Middle Attack: Set up a network and attempt to perform a man-in-the-middle attack. Observe how the attacker can intercept and manipulate network traffic. Then, implement security measures (like encryption) to prevent this type of attack.
-
Scenario 3: Protecting a Server: Create a network with a critical server. Implement multiple layers of security, including firewalls, ACLs, and intrusion detection mechanisms, to protect the server from various types of attacks. Experiment with different attack vectors and see how your security measures hold up.
-
Scenario 4: Implementing VPN for Remote Access: Create a network and configure a VPN connection for remote access to specific resources. Test the security of the VPN connection by attempting to intercept the traffic.
-
Scenario 5: Wireless Network Security: Configure a wireless network with robust security measures (WPA2/WPA3 if available). Attempt to crack the wireless password using various attack methods (dictionary attack) to highlight the importance of strong passwords and security protocols.
Going Beyond the Basics: Extending Your Learning
While Packet Tracer 3.11.1 provides a solid foundation, it's important to supplement your learning with additional resources.
-
Research real-world security incidents: Understanding how real-world attacks are executed can provide valuable context and improve your understanding of network security principles.
-
Explore advanced topics: Once you're comfortable with the basics, delve into more advanced topics such as network forensics, cryptography, and security auditing.
-
Stay updated with current trends: The cybersecurity landscape is constantly evolving, so staying current with new threats and vulnerabilities is crucial. Follow industry news and attend relevant conferences.
-
Practice, practice, practice: The more you practice with Packet Tracer and other tools, the better you'll become at identifying and mitigating security risks.
Conclusion: Mastering Network Security with Packet Tracer 3.11.1
Packet Tracer 3.11.1, despite its age, remains a valuable tool for understanding fundamental network security concepts. By practicing the scenarios outlined above and continuously expanding your knowledge, you'll build a strong foundation in network security, preparing you for more advanced studies and a career in the field. Remember, continuous learning and hands-on experience are key to mastering the ever-evolving world of network security. Use Packet Tracer 3.11.1 as a springboard to explore the fascinating and crucial world of cybersecurity.
Latest Posts
Latest Posts
-
Radioactive Dating Game Lab Answer Key
Apr 03, 2025
-
3 02 Quiz Linear And Quadratic Systems
Apr 03, 2025
-
In Addition To A Lower Salary Business Compensation Structures
Apr 03, 2025
-
Pmcs Test Is Conducted In Which Phase Of Training
Apr 03, 2025
-
Categorize Each Scenario As Describing A Movement
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about 3.11.1 Packet Tracer - Network Security Exploration . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
